Key Takeaways
- Invisible threat: Shadow IT includes all IT systems, cloud services, and AI tools that employees use without approval.
- The causes of shadow IT: Shadow IT emerges from a lack of alternatives, slow approval processes, and gaps in onboarding.
- Structure over control: Only the combination of technical transparency, fast approval processes, and user-friendly solutions permanently removes the conditions that shadow IT thrives on.
- deeploi as the solution against shadow IT: Central device management, automated on- and offboarding, and software deployment through one platform give companies full visibility again.
Shadow IT: identify the risks and avoid them for good
An HR manager is preparing the offboarding of an employee and discovers that he has been using dozens of cloud services, AI tools, and SaaS solutions. Nobody in IT knew about them. Nobody approved them. And nobody knows what's happening to the data still sitting there.
Shadow IT is a symptom of missing IT structure, and it grows in every organisation that lacks clear processes for tool approval, onboarding, and device management. The solution isn't bans – it's lasting transparency and simple IT governance. That's exactly what deeploi delivers as an ISO 27001-certified all-in-one IT platform, already trusted by over 250 companies without their own IT department.
What is shadow IT and why does it affect so many companies?
Shadow IT describes all hardware, software, cloud services, and AI tools that employees use without the knowledge or approval of the responsible IT function. Whether it's a personal cloud storage account, a self-installed app, or a ChatGPT account for daily work – it all counts. One insight is key here: shadow IT almost never stems from malicious intent. It's the result of a desire for efficiency, functional gaps in official IT solutions, and a lack of alternatives.
In everyday work, shadow IT shows up in many forms that seem harmless at first glance:
- Personal Dropbox or Google Drive accounts where company and customer data ends up
- WhatsApp groups used for client communication or internal coordination
- ChatGPT plugins and other AI tools without any IT approval
- Self-configured Trello or Notion boards for project management
- Personal devices connected to the corporate network
SMEs with 30–200 employees are particularly affected. The reason: there's often no dedicated IT team. Instead, HR managers, office leads, or founders handle IT responsibilities on the side – the so-called accidental IT owners. Without systematic asset tracking, there's no visibility into which tools are actually in use.

Shadow IT takes various forms: shadow SaaS (unapproved software-as-a-service applications), shadow AI (uncontrolled use of AI tools like ChatGPT or Copilot), citizen development (independently built workflows using no-code tools), and BYOD (personal devices used for work). Each of these carries its own risks for security, data protection, and compliance.
The real causes of shadow IT in organisations
Shadow IT doesn't emerge from bad intent – it's the logical response to structural problems that slow employees down every day. Understanding the causes enables targeted action, rather than just treating symptoms.
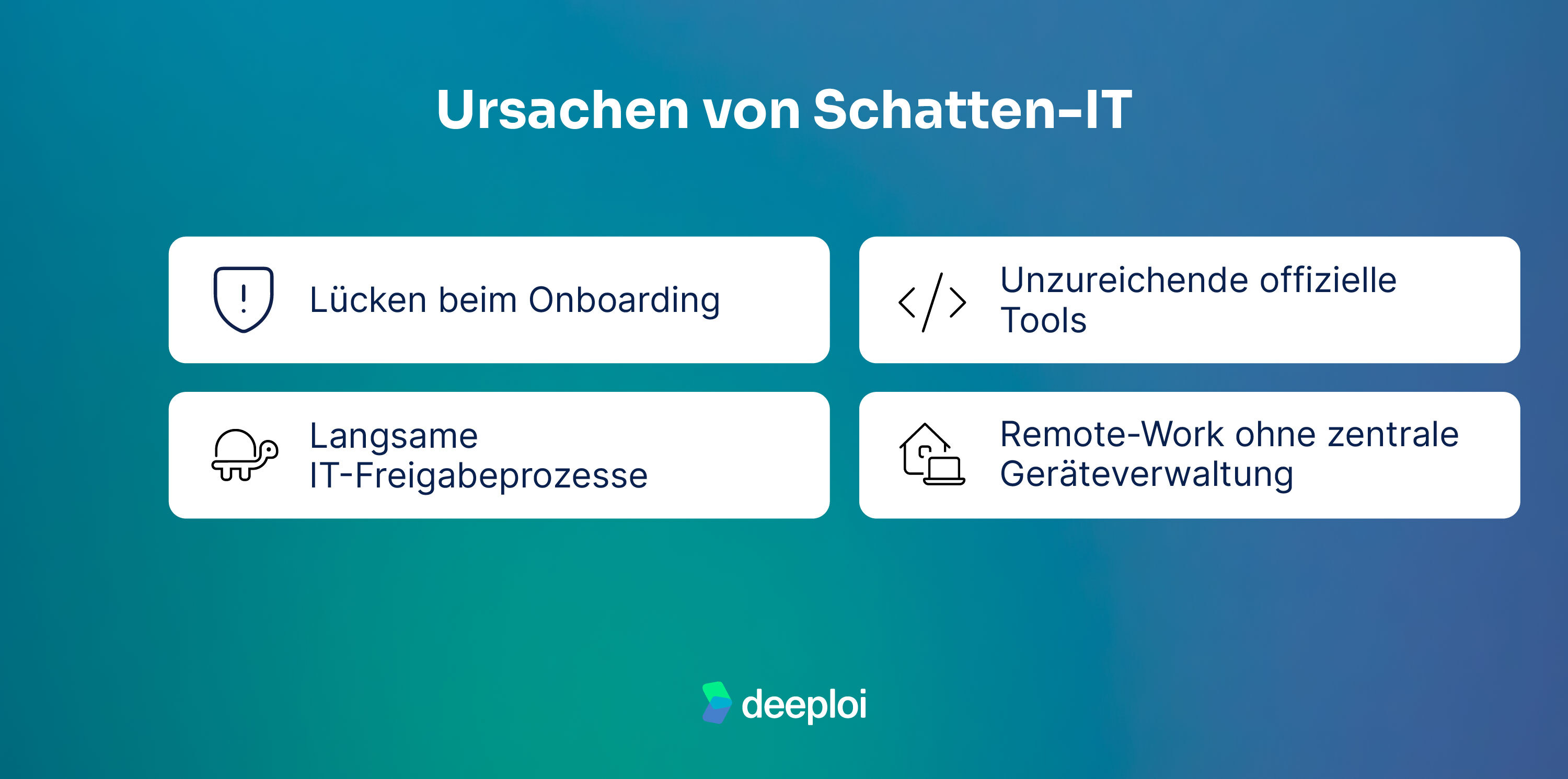
Onboarding gaps
The most common entry point for shadow IT is the first day of work. HR has signed the contract, the welcome pack is ready. But the laptop isn't configured, software access is missing, and the email account doesn't exist yet. The gap between HR onboarding and IT provisioning is structurally embedded in many organisations, because the two processes aren't synchronised.
The natural response from new employees? Bring their own devices, use personal cloud services like Google Drive, or set up a personal ChatGPT account. What starts as an improvised pragmatic fix quickly becomes habit.
Automated onboarding processes close exactly this gap before shadow IT even has a chance to emerge.
Shadow IT starts on day one. Close the gap with deeploi.New employees ready to go in 3–5 minutes, with all approved apps, access, and devices from day one.Close security gaps now →
Slow IT approval processes
If a tool request takes two weeks to get approved, no sales rep will wait for the official solution. They'll simply sign up themselves – free of charge, in two minutes. This is exactly where shadow IT begins: not out of bad intent, but out of an efficiency problem. The slower and more bureaucratic the official route, the more attractive the unofficial one becomes.
Inadequate official tools
Employees turn to their own solutions when the tools provided don't reflect their actual day-to-day work. A design team working with an outdated project management tool switches to Notion or Figma because they want to be more productive. In cases like these, shadow IT is direct feedback to IT: the official solutions don't fit.
Remote work without central device management
Working from home has accelerated shadow IT. When people work remotely, they solve IT problems themselves – because there's no IT department on site. Personal devices end up on the corporate network, personal cloud storage replaces approved file shares, and browser extensions get installed without review. Without central device management, IT simply has no visibility into what's running on which device, or where company data is actually ending up.
The numbers confirm the picture: 80% of employees use shadow IT for convenience and productivity reasons (Syteca). At the same time, a HP study found that 39% of younger employees said they didn't know their company's data security policies well enough – and 54% of that group prioritised meeting deadlines over avoiding security risks (HP Wolf Security). Using unapproved tools is less a knowledge problem than a supply problem.
The hidden costs of shadow IT
While the obvious risks like security gaps are easy to spot, three cost dimensions often stay invisible: uncontrolled software spend, regulatory fines, and the downstream costs of data breaches. Together, they create a risk profile that many companies massively underestimate.
The situation becomes especially critical during offboarding. When employees leave and nobody knows which unapproved tools they were using, access stays active. App permissions and accounts with cloud services that were never inventoried represent a permanent security risk. Without a central overview of all applications in use, a clean offboarding is simply impossible.
Do you know which tools your team is using right now?Over 250 companies have regained full visibility with deeploi – without their own IT department.Avoid IT shadow risks now →
From sprawl to structure: systematically containing shadow IT
Eliminating shadow IT entirely is unrealistic. But reducing it to a manageable level is absolutely achievable. The key lies in a two-pronged approach: technical detection methods uncover existing shadow IT, while organisational measures prevent it from arising in the first place.
Tracking down unapproved cloud services and AI tools
Before you can contain shadow IT, you need to know where it exists. These four detection methods give you the full picture:
Network monitoring and traffic analysis: Systematically analysing network traffic quickly reveals which applications are actually in use – including those nobody officially approved.
Firewall and proxy log analysis: Logs contain valuable clues about unapproved tools. Many companies already have this information – it's just rarely reviewed proactively.
Cloud Access Security Broker (CASB): A CASB sits as a control layer between users and cloud services, detecting unauthorised access in real time.
Employee surveys: Asking directly which tools the team actually uses gives you an initial overview and creates the foundation for targeted technical measures.
One important note: a CASB alone isn't enough. It only captures cloud traffic. Locally installed software or AI tools accessed via mobile data remain invisible. Real transparency only emerges in combination with endpoint management.
Setting up IT policies and approval processes correctly
A shadow IT policy only works when it's paired with fast, low-friction alternatives. Anyone waiting weeks for approval will find their own solution. A risk-based tiered model helps solve this problem:
Central device management as the foundation against IT sprawl
Without a central inventory, nobody knows which devices and software are actually in use. This is exactly where a central platform for MDM, software deployment, and patch management comes in. It forms the structural foundation that makes detection and policies effective in the first place.

deeploi's device management creates exactly this transparency: automatic policy enforcement, a central inventory of all IT assets, and a platform dashboard that gives accidental IT owners full oversight.
Why strict IT policies fail without alternatives
Many organisations respond to shadow IT with strict bans. This sounds decisive, but achieves the opposite: employees don't use the tools less – they use them more secretly. IT loses all visibility, and the actual risk increases. Bans drive usage underground and make control impossible.
The more effective approach is empathetic rather than restrictive: positioning IT as an enabler rather than a control function. Providing fast, low-friction alternatives and speeding up approval processes makes shadow IT simply unnecessary. Employees don't reach for their own tools because they want to break rules. They do it because the official IT solutions don't support their day-to-day work.
Avoiding shadow IT with deeploi
Onboarding gaps, tool sprawl, and missing transparency are the three main drivers of shadow IT. All three can be systematically addressed with a central platform. deeploi was built as an all-in-one IT platform for exactly this purpose: companies regain control over their entire IT infrastructure without needing to build in-house IT expertise.
Automated onboarding in 3–5 minutes: New employees receive ready-to-use devices with all approved apps and access from day one. The gap where shadow IT typically emerges simply no longer exists.
Central software management with approved app bundles: Instead of sprawl from self-installed tools, there's an approved software catalogue that's automatically rolled out via the platform.
Platform dashboard with full asset transparency: All devices, software, and access rights at a glance. Accidental IT owners stay in control without having to navigate complex IT systems.
Security at offboarding: deeploi automatically revokes all access and deploys remote lock and wipe. Orphaned accounts, over-privileged app permissions, and forgotten cloud services become a thing of the past. No manual tracking, no risk from former employees.

deeploi combines this automation with an expert helpdesk that responds in an average of 12 minutes (SLA: 30 minutes). Whether you're an HR manager, ops lead, or founder: you implement IT governance without needing to be an IT expert yourself. The platform handles the technical complexity while you focus on your core business.
Conclusion: shadow IT ends where transparency begins
Shadow IT is a structural risk with growing legal consequences – from GDPR fines to personal executive liability under NIS2. But the solution isn't bans. Organisations that invest in transparency, fast approval processes, and central device management permanently remove the conditions that shadow IT needs to thrive.
For SMEs without their own IT department in particular, an all-in-one platform like deeploi is the most practical path: IT control without additional headcount, without deep IT knowledge, and without compromising on security and compliance. Addressing the root causes rather than fighting symptoms makes shadow IT redundant.
FAQ
What legal consequences can shadow IT lead to?
Shadow IT can result in GDPR fines of up to 4% of annual revenue if personal data is processed in unapproved tools. Under NIS2, additional fines of up to €7 million apply – and executives face personal liability under §38 BSIG, even without personal fault. On top of that, the downstream costs of data breaches: incidents involving shadow AI cost companies an average of over $5 million (IBM 2025).
Does shadow IT affect small companies without an IT department?
Yes – SMEs without a dedicated IT team are particularly vulnerable. When nobody has an overview of the tools and cloud services being used, shadow IT grows unnoticed. A central IT platform like deeploi can replace the missing IT department and create the necessary visibility across all devices, software, and access rights.
What can I do about shadow IT in concrete terms?
Three immediate measures have the fastest impact: conduct an inventory of all tools in use, set up fast approval processes with secure alternatives, and implement central device management with automated on- and offboarding. deeploi covers all three steps through a single platform.
How do I handle uncontrolled AI use in my organisation?
Bans don't work against uncontrolled shadow AI – providing secure alternatives does. Through central IT asset management, companies maintain full transparency over software in use and prevent dangerous data gaps at offboarding. This turns uncontrolled usage into a secure, productive IT strategy that combines data protection and efficiency.